Othmen Mhiri
I’m an IT student at ISET Sousse specializing in Networks and IT Services.
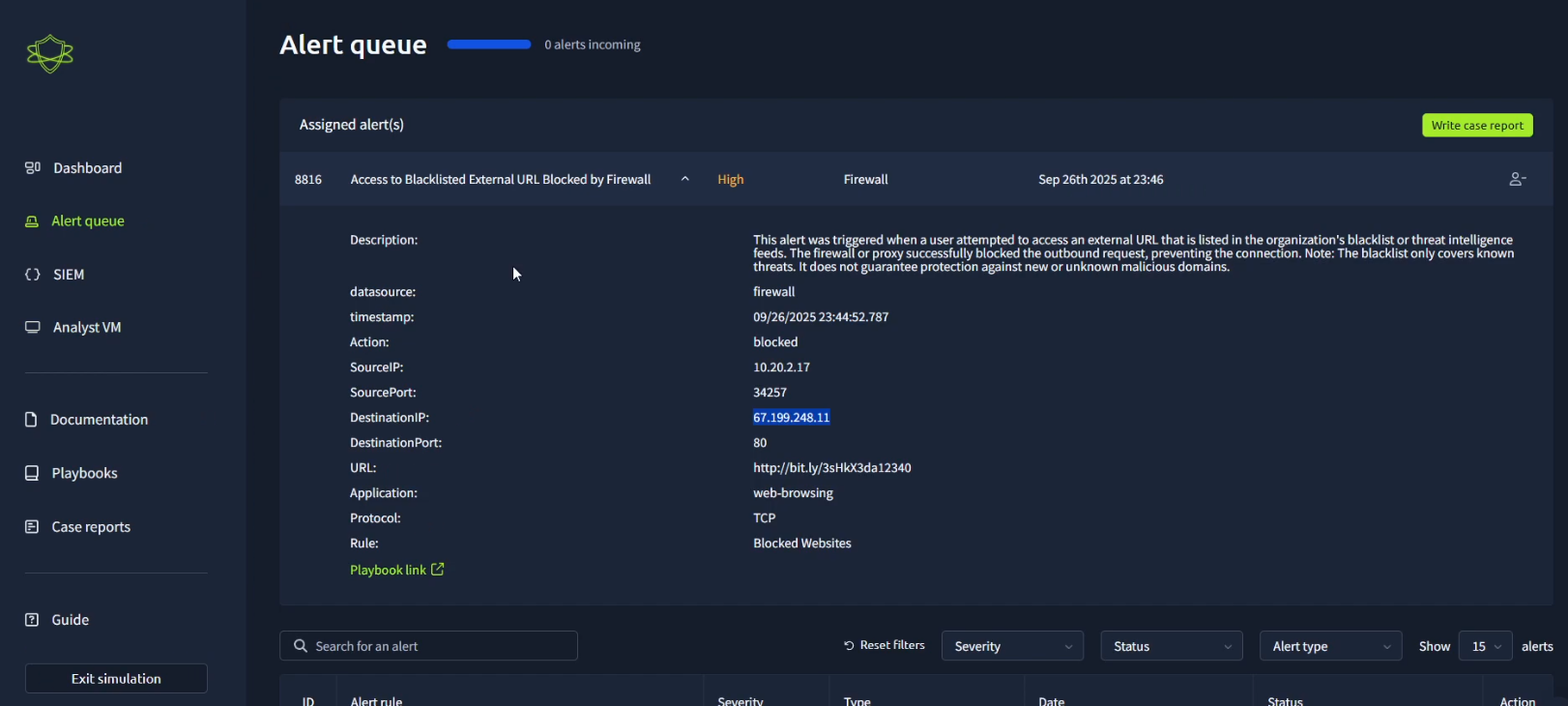
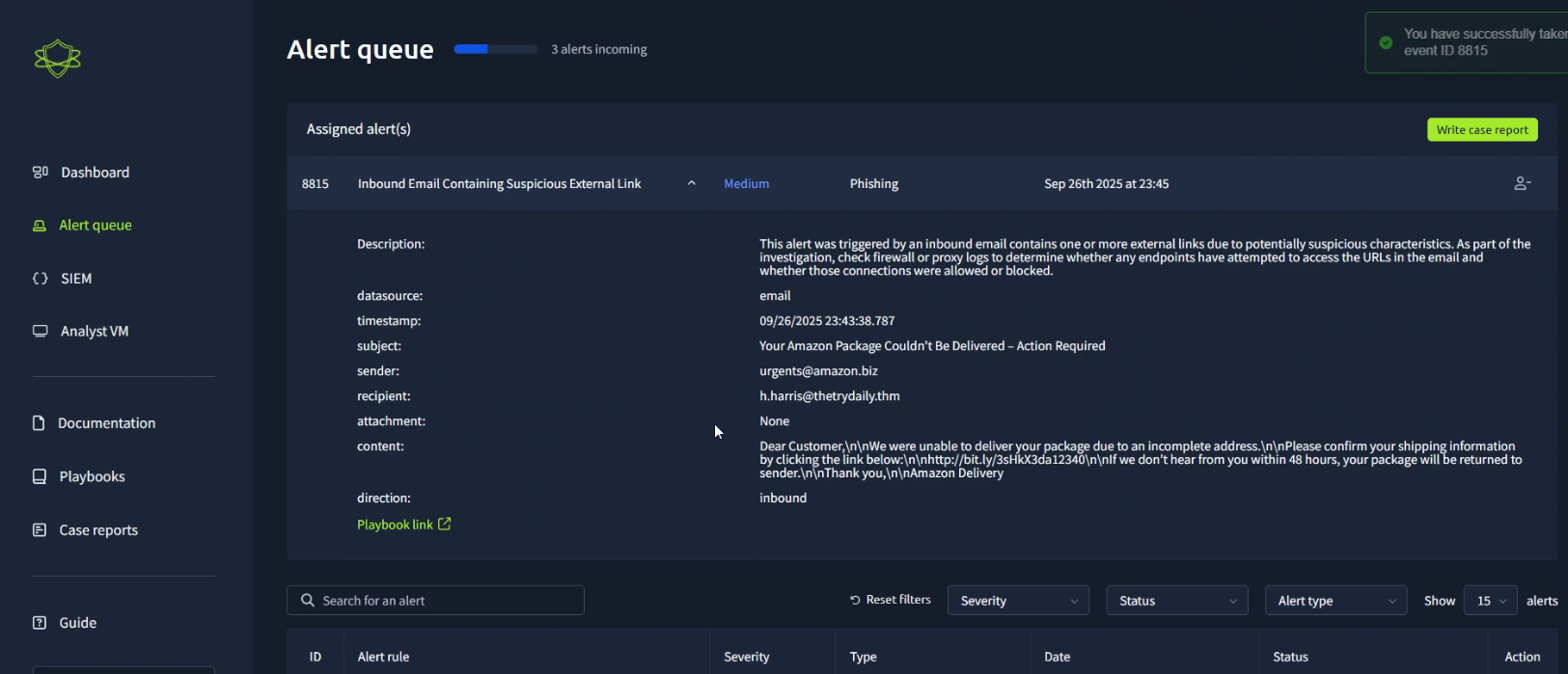
Currently focusing on Cloud Computing, DevOps, and Cybersecurity while building hands-on projects and strengthening real-world skills through internships.
I’m putting in the work now to grow and build my career internationally.